1. The New Era of Telecom Data Monetization Is Here
The global telecommunications landscape is undergoing a fundamental shift. For decades, the primary value of a mobile network was connectivity. Today, that value is shifting toward number intelligence. Telecom operators and Communications Platform as a Service (CPaaS) providers are sitting on a goldmine of daily traffic data that, until recently, remained largely unutilized. Number Risk Scoring is the key to unlocking this potential.

At its core, Phone Number Risk Scoring is both a strategic and commercial move. It allows telcos to monetize their internal data by providing enterprises with real-time identity and reputation signals, leveraging Machine Learning and AI. Unlike traditional verification methods that only look at a single point in time, this solution analyzes behavioral history and traffic patterns to distinguish legitimate human users from sophisticated fraudulent bots, ill-intentioned human fraudsters, and scammers.
By transforming everyday messaging and voice traffic into actionable number-risk scores, telcos can create a high-margin revenue stream while becoming essential partners in the global digital economy. Let’s dive a little deeper.
2. Solving the Enterprise Crisis
As digital onboarding becomes the norm, enterprises are facing a surge in automated and AI-accelerated fraud that traditional security measures fail to catch. Phone Number Risk Scoring acts as a silent, frictionless shield that addresses three of the most expensive pain points in the B2C space. Let’s look at three popular examples.
2.1 Social Media and the Bot-Influencer Epidemic
Social media platforms like Reddit, TikTok, Discord and Instagram are in a constant battle against bot registrations. These non-human accounts are used to artificially inflate view counts and engagement metrics, which directly devalues the platform for legitimate advertisers.
By analyzing the recency, velocity and other methods of a number’s historical activity, Number Risk Scoring identifies the numbers showing bot behaviors before they can even register, ensuring that the user base remains genuine and human.
2.2 Banking and the Battle Against Account Takeover
Financial institutions are high-stakes targets for Account Takeover (ATO) attacks. Fraudsters often use disposable Voice over IP (VoIP) numbers or SIM card swapping to gain unauthorized access to sensitive accounts.
A bank can use Number Risk Scoring to detect using line types and other behavioral data associated with a phone number. If a number shows a sudden burst of activity after months of silence, the bank can interpret this as a risk signal and block the transaction before a breach occurs.
2.3 E-Commerce and Hit-and-Run Promo Abuse
Growth-focused e-commerce platforms often lose millions to promotional abuse, where fraudsters create thousands of accounts to exploit “new user” discounts or referral bonuses. These “hit-and-run” attackers use fresh numbers with no behavioral history.
Number Risk Scoring allows an e-commerce platform to see if a number has a long-term, human-like footprint. If a number lacks a history of successful P2P (person to person) communication, the platform can flag it as a bot, protecting their marketing budget for real, loyal customers.
3. The Solution: Number Risk Scoring as a Real-Time, Frictionless Shield
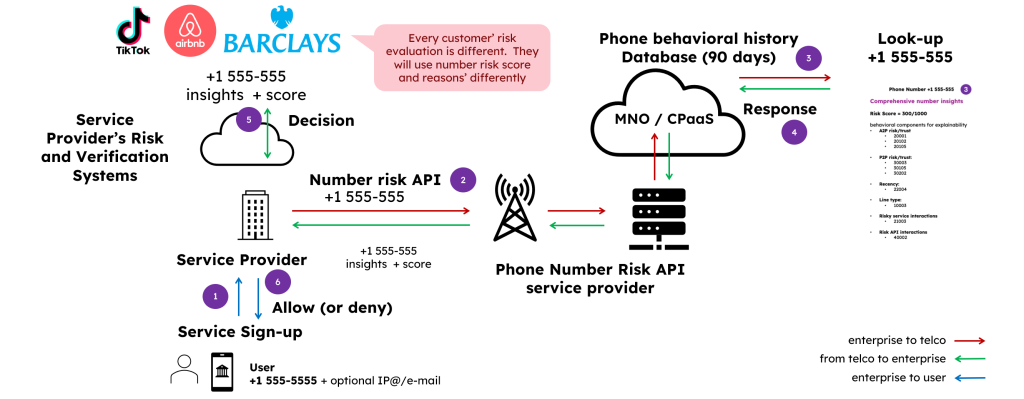
Number Risk Scoring functions as a sophisticated intelligence layer that operates entirely in the background of a digital transaction. When a user enters their phone number on a website or app, the enterprise triggers a request that analyzes the historical footprint of that specific number. This process happens in milliseconds, ensuring that legitimate users experience zero friction while fraudulent actors are met with an invisible barrier.
The true power of this solution lies in its ability to differentiate between human and non-human or human-with-ill-intent behavior through long-term analysis. By looking at a 90-day window of activity, the system identifies patterns that a single “snapshot” verification would miss.
For example, a genuine human user typically has a consistent history of successful message deliveries and voice calls, whereas a bot or a “burner” number used for fraud often shows erratic, high-velocity activity followed by long periods of dormancy.
3.1 Each enterprise defines its own risk thresholds
A critical aspect of the Number Risk Scoring business model is that the data is managed by the telcos and accessed via an API request by the enterprise. However, the telco does not unilaterally decide who is “good” or “bad.” Instead, the telco provides the raw behavioral signals and a reputation score, but each enterprise defines its own risk thresholds.
This flexibility is where the business model truly excels. A risk-averse bank might block any number classified as a Voice over IP (VoIP) line type, while a growth-oriented social media platform might choose to allow that same number if it shows human-like behavioral history over the last three months. The enterprise remains in control of the user journey, using telco intelligence to fuel their internal risk engines.
3.2 The Data Building Blocks: CDRs and Traffic Patterns
To build an accurate risk profile, the system aggregates several layers of internal and external data. The foundation consists of Call Detail Records (CDRs), which provide a view of Application-to-Person (A2P) and Person-to-Person (P2P) traffic. Here is the full overview of all the types of data sources that can come into play for number risk scoring:
- Telco Data: Includes network logs, A2P/P2P SMS traffic, voice traffic, SIM swap signals, and location via CAMARA APIs, among others.
- 3rd-Party Data: Enriches insights with IP address intelligence, email intelligence, and fraud databases.
3.3 A Complementary Layer in the Verification Stack
It is important to clarify that Number Risk Scoring is not intended to replace existing identity verification methods. Instead, it serves as a powerful complement to legacy tools like SMS OTP and newer methods like Silent Authentication (Network APIs).
While Silent Authentication confirms that a SIM card is currently active and linked to an IP address, Number Risk Scoring explains the behavior behind that SIM. By using both, an enterprise can confirm that a user is who they say they are and that they have a history of trustworthy activity. This multi-layered approach provides a much higher level of assurance than any single API could offer on its own.
3.4 Security and Privacy by Design
In an era of strict data protection regulations such as the GDPR, Number Risk Scoring offers a privacy-by-design alternative to traditional data sharing. The value proposition of Global Telco Consult is bringing the machine learning model directly into the telco’s secure data center environment.
Because the model stays internal to the operator, sensitive raw data never needs to leave the telco’s infrastructure. The enterprise only receives a machine-readable risk signal or a numerical score.
Furthermore, user consent is typically gathered upfront during the sign-up process, where the enterprise informs the user that a background check will be performed for fraud prevention and identity verification purposes. This ensures a fully compliant and secure exchange of intelligence.
4. The Telco Business Case: High Margins at Competitive Prices
The shift toward Number Risk Scoring is one of the most compelling business cases for modern telecommunications operators today. By leveraging data that is already being generated every single day, telcos can transition from being passive bit-pipers to active participants in the high-value identity and fraud prevention market.
4.1 The (Very) High Margin Model
The economics of Number Risk Scoring are typically superior to external network APIs or traditional SMS delivery network investment. Because the operator utilizes its own internal, everyday generated data, the primary costs are shifted away from data acquisition and toward the initial building and deployment of the machine learning model.
With the decreasing cost of cloud compute and more efficient algorithms, the direct margins for this service are remarkably high, typically above 70%. This allows telcos to turn an operational byproduct—traffic metadata—into a profit center.
4.2 Rich Data as a Competitive Edge
One of the most significant advantages for a telco is the ability to offer a versatile service that adapts to various enterprise needs. Unlike a one-size-fits-all single purpose service, Number Risk Scoring offers versatility and multiple use-cases.
A telco can provide the same raw behavioral signals to a bank, a social media platform, and an e-commerce site, and each applies its own logic to extract the data and insights it needs. This data-rich and flexible approach creates a deeper, more “sticky” relationship with the enterprise, as the telco becomes a foundational part of the customer’s internal risk engine.
4.3 Competitive Positioning and Market Growth
Because the underlying cost of generating these risk signals is low, telcos can offer Number Risk Scoring at a very competitive price point. In many markets, this service can be positioned as a more cost-effective alternative to high-volume SMS verification while providing significantly more intelligence.
Furthermore, as established in section 3.3, this is a highly complementary service. Telcos do not have to choose between selling SMS, network APIs, and selling risk scores; they can offer a layered security package. By bundling identity verification with behavioral insights, operators provide a level of assurance that third-party aggregators cannot match. This makes Number Risk Scoring a strategic move for any telco looking to maximize the value of its data and secure its place in the future of digital trust.
Conclusion: Mastering the Complexity of Number Risk Scoring with GTC
Entering the number risk scoring space is a journey that requires more than just big data and data science. The Global Telco Consult (GTC) team is uniquely positioned to guide Mobile Network Operators (MNOs) and CPaaS players through this transition. We understand that the transition from a connectivity provider to a data intelligence powerhouse does not happen overnight.
GTC utilizes a proven, step-by-step model designed to help our partners ascend the ladder of complexity at a sustainable pace. By starting with foundational use cases and simple risk models, we allow providers to gain immediate experience and generate early revenue.
As the partnership matures, we help unlock new layers of capabilities, moving from basic rule-based signals to highly sophisticated machine learning behavioral analysis. This gradual approach mitigates risk while steadily increasing the value and profitability of the telco’s data assets.
Our support covers the full cycle of mastery in number risk scoring. GTC provides end-to-end guidance across every critical pillar:
- Planning and Strategy: Defining the business case and identifying the most lucrative local use cases.
- Model Training, Development, Deployment: Upskilling internal teams to understand the nuances of behavioral signals and explainability.
- Org Design, Hiring and Resource Alignment: Helping you build the right internal team of data scientists and product experts.
- Go-to-Market Execution: Crafting the commercial strategy to pitch these services competitively to banks, social media platforms, and e-commerce giants.
Initiate a number risk scoring discussion with one of our experts here.
